The State of Cybersecurity 2023.
In the last 4 weeks Sophos – with whom Fusion are a Sophos Gold Partner – have released their ‘The State of Cybersecurity 2023’ Report. Please take a look at the below video for a taster and then the infographic for the Key Findings.
State of Cybersecurity 2023: The Business Impact of Adversaries from Sophos on Vimeo.
Key Findings
In addition to the top-level findings above the following insightful points were also made.
In 2023, nearly all IT professionals express worry over cyberthreats that could impact their organisation. According to their concerns, data exfiltration, which refers to external attackers stealing sensitive data, ranks as the top threat. Following closely behind is phishing, including spear phishing, while ransomware occupies the third spot in the list of IT professionals’ concerns. It is noteworthy that these top three threats often intertwine. Typically, a cyberattack begins with a phishing email, leading to data exfiltration and culminating in a ransomware attack.
IT professionals’ concerns closely align with the reality of cyberattacks experienced by organisations. In the last year, 94% of organisations have encountered at least one cyberattack, with ransomware being the most commonly reported. Adversaries execute a range of attacks on a large scale, creating an extensive and increasing challenge for defenders.
Behind these statistics lies the escalating ‘professionalisation of the cybercriminal economy’, which includes the emergence of the ‘as a service’ model, such as ‘access-as-a-service,’ ‘phishing-as-a-service,’ and ‘scamming-as-a-service.’ This transformation in cybercrime operations has significantly reduced the barriers to entry for aspiring cybercriminals.
The Rise of Active Adversaries
One key area of concern is the rise of Active Adversaries.
Active adversaries are threat actors who possess the ability to adapt their techniques, tactics, and procedures (TTPs) on the fly, leveraging real-time hands-on-keyboard actions to respond to security technologies and defenders’ actions, and evade detection. These attacks frequently lead to devastating ransomware and data breach incidents, making them incredibly difficult to prevent.
In the previous year, 23% of respondents disclosed that their organization faced an attack from an active adversary. The attack rate remained consistent across all organization sizes, differing by only two percentage points in all segments. Interestingly, for organizations with an annual revenue of less than $10 million (approx £8 million) , the rate of reported active adversary attacks decreased to just 11%, implying that attackers may deliberately target more financially robust entities. Detecting active adversaries necessitates a high level of skill, making it likely that the actual incidence rate is higher.
Given the potential destruction of these attacks, 30% of respondents consider active adversaries as one of their primary cyberthreat concerns for 2023.
Can’t We Just Block these Active Adversaries?
No.
To comprehend the challenge that defenders face, it is crucial to understand that merely blocking active adversaries is insufficient in thwarting their efforts. These highly skilled and persistent threat actors employ multiple techniques, tactics, and procedures (TTPs) to accomplish their objectives, which include:
- Exploiting security vulnerabilities to infiltrate organisations and move laterally within the network, leveraging stolen credentials, unpatched vulnerabilities, and misconfigured security tools.
- Taking advantage of legitimate IT tools utilised by defenders to avoid triggering detections.
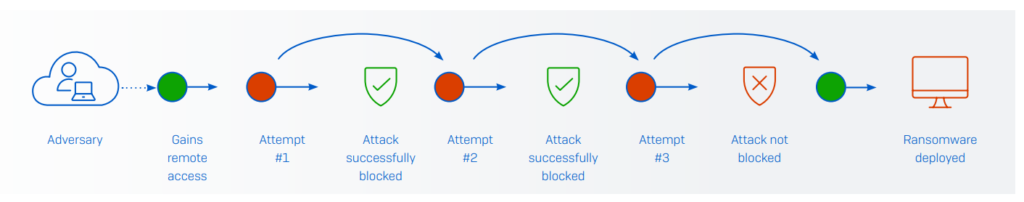
- Adjusting their attacks in real-time in response to security controls, continuously pivoting to new techniques until they discover a way to achieve their goals as illustrated below.
And there’s more to Worry About!
Misconfiguration of Security Controls
The most commonly perceived security risk is the misconfiguration of security controls (such as an endpoint or firewall solution), with 27.4% of respondents identifying it as one of their top three cyber risks. This ranking highlights the difficulties faced by IT teams in ensuring that their security controls remain correctly configured and deployed at all times, and how easily adversaries can exploit any gaps in an organisation’s defenses.
In second place are zero-day attacks, which exploit previously unknown security vulnerabilities or software flaws, and were rated as a top three security risk by 26.8% of respondents. A shortage of in-house cybersecurity skills and expertise came in third on the list, with 25% of respondents rating it as a top three security risk.
There is a direct correlation between the shortage of skills and security tool misconfiguration: without the time, knowledge, and experience required to configure controls correctly, gaps in defenses are created.
The Challenge of Alert Investigation
Defenders face the challenge of determining which alerts require investigation and how to optimise their limited resources for the best results. On average, 48% of all security alerts are investigated to determine if they indicate malicious activity, with this number increasing to 54% in organizations with 3,001-5,000 employees. However, approaches to investigations vary greatly: 16% of organizations investigate over three-quarters of their alerts (including 5% who investigate all alerts), while 18% investigate only a quarter or less of their alerts.
Security Skills Shortage
The shortage of in-house cybersecurity skills/expertise is considered one of the top security risks for 2023 by IT professionals. However, the survey indicates that organisations are struggling with day-to-day security operations tasks. A significant 93% of respondents find at least one of the following activities challenging:
- Identifying signals from noise (71% find challenging)
- Prioritising which signals/alerts to investigate (71% find challenging)
- Obtaining sufficient data to determine if a signal is malicious or benign (71% find challenging)
- Remediating malicious alerts or incidents in a timely manner (71% find challenging)
- Identifying the root cause of the incident (75% find challenging)
- Keeping accurate records of investigations (68% find challenging)
- The most widespread issue is identifying the root cause of the incident, with 75% of respondents reporting that they find it challenging.
Defenders Out of Their Depth
More than half (52%) of IT professionals acknowledge that their organisation is incapable of handling cyberthreats on its own due to their advanced nature. This percentage increases to 64% among small businesses with 100-250 employees. As the organisational revenue grows, the probability of in-house teams being unable to keep pace also increases. This trend possibly indicates the more intricate internal cybersecurity environment in larger revenue organizations and a higher likelihood of involving specialised security services. It might also signify a greater comprehension of the threat landscape and the complexities involved in safeguarding against advanced threats.
So What Can Be Done?
To effectively address cybersecurity threats, a three-step approach is recommended.
- Firstly, organisations should implement a more scalable incident response process that speeds up response time.
- Secondly, they should use adaptive defenses to slow down adversaries.
- Thirdly, they should create a virtuous cycle that improves protection and lowers cost. This can be compared to the concept of “Shields Up,” where organisations optimise the efficacy of their defenses by using context-sensitive technologies to elevate protection levels based on the situation.
The quality of cybersecurity technologies is crucial, and organisations should optimise prevention by automatically detecting and stopping as many threats as possible early in the attack chain. They should also reduce exposure by ensuring that security investments are correctly deployed and avoid misconfiguration issues. Furthermore, technologies that automatically detect and disrupt adversarial activity can frustrate attackers while buying defenders time to neutralize the incident.
Although shields provide valuable time for defenders to investigate and respond to attacks, they do not guarantee 100% prevention. Timely, well-informed, and well-executed root cause remediation is essential. Leveraging telemetry from across the security environment enables Defenders to see and respond to threats faster while increasing return on existing investments. Processing signals through an Extended Detection and Response (XDR) platform that adds contextual insights and correlates related alerts enables in-house defenders to quickly focus on what’s important. Alternatively, organisations can outsource detection, investigation, and response work to a specialist Managed Detection and Response (MDR) service.
Thanks
Richard